NHS “Wanna Decryptor” Ransom Hack: The Facts
[et_pb_section bb_built=”1″ admin_label=”Section” transparent_background=”off” allow_player_pause=”off” inner_shadow=”off” parallax=”off” parallax_method=”off” custom_padding=”0px|0px|0px|0px” padding_mobile=”off” make_fullwidth=”off” use_custom_width=”off” width_unit=”on” custom_width_px=”1080px” custom_width_percent=”80%” make_equal=”off” use_custom_gutter=”off” fullwidth=”off” specialty=”off” disabled=”off”][et_pb_row admin_label=”Row” make_fullwidth=”off” use_custom_width=”off” width_unit=”off” custom_width_px=”1080px” custom_width_percent=”80%” use_custom_gutter=”off” gutter_width=”3″ custom_padding=”0px|0px|0px|0px” custom_padding_tablet=”0px|0px|12px|0px” padding_mobile=”off” allow_player_pause=”off” parallax=”off” parallax_method=”on” make_equal=”off” column_padding_mobile=”on” parallax_1=”off” parallax_method_1=”on” parallax_2=”off” parallax_method_2=”on” parallax_3=”off” parallax_method_3=”on” parallax_4=”off” parallax_method_4=”on” disabled=”off”][et_pb_column type=”4_4″][et_pb_post_title admin_label=”Post Title” title=”on” meta=”on” author=”on” date=”on” date_format=”M j, Y” categories=”on” comments=”off” featured_image=”on” featured_placement=”background” parallax_effect=”off” parallax_method=”on” text_orientation=”left” text_color=”dark” text_background=”on” text_bg_color=”rgba(70,213,195,0.74)” module_bg_color=”rgba(70,213,195,0.43)” title_font=”|on|||” meta_text_color=”#000000″ use_border_color=”on” border_color=”#46d5c3″ border_width=”18px” border_style=”solid” disabled=”off” meta_font=”|on|||” /][/et_pb_column][/et_pb_row][/et_pb_section][et_pb_section bb_built=”1″ admin_label=”section”][et_pb_row admin_label=”row”][et_pb_column type=”4_4″][et_pb_text admin_label=”Text” background_layout=”light” text_orientation=”left” use_border_color=”off” border_color=”#ffffff” border_style=”solid”]
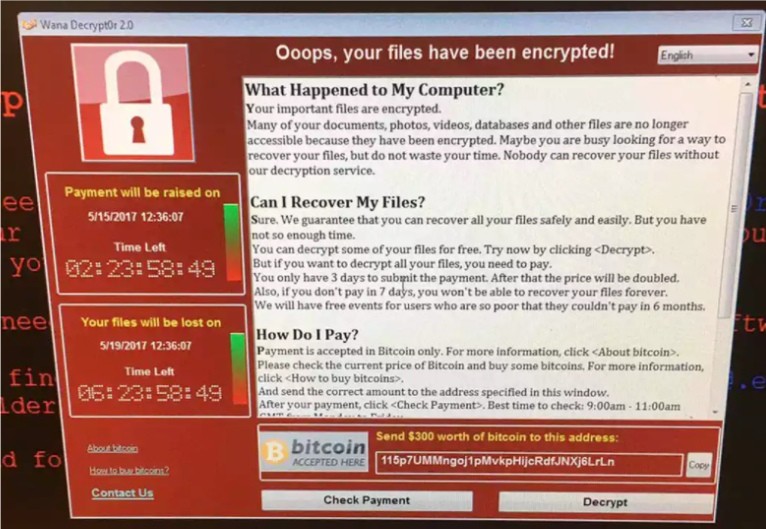
Today the NHS fell victim to a ransom hack by the “Wanna Decryptor” virus. A large number of NHS trusts have been affected by the virus that has disrupted services, and harmed patient care. The ransom hack demanded payment in the form of bitcoin, a digital currency to end the ransom.
The Clinical Developers Club have written a brief guide for clinicians on the attack, and what they can do about it.
The technical details
This is a ‘ransomware’ virus- files are reversibly encrypted using a secure key- the same method that protects your online banking from being viewed by anyone else with the connection, is now being misused to lock files until a ransom is paid. The encryption cannot be reversed without the key.
The virus uses a vulnerability in the Windows operating system, first researched by the NSA, and leaked last year as part of the NSA ‘hack’ [1] . A patch was deployed by Microsoft 2 months ago to prevent an attack just of this sort [2] . Just as the child who presents with measles, we must ask- why did these NHS trusts not opt for their digital vaccinations?
Why the NHS?
It’s likely that this is not a targeted attack. NHS trusts are not the only places affected, and thousands of other businesses are also reporting the intrusion in 74 countries [3] . Quite possibly the authors of the virus aimed to target a number of small businesses, and never expected to get into such a large target as the NHS, and the legal attention that will undoubtedly follow.
Questions for NHS England
- Why did 25 NHS trusts not deploy the recommended Microsoft patch, 2 months after it’s release?
- Are only ‘terminal’ level computers affected, or are any data centres compromised?
- What is the backup policy? Backing up files regularly will still result in data loss but the effect will be reduced as the information can be recovered from a previous backup.
Information for clinicians
The key thing to take note that this is not compromised by personal devices like mobile phones. Due to the shock of the problem there might be some managers suggesting bans on electronic devices. USB flash drives have been implemented in attacks in the past, one of the most famous being Stuxnet, a computer worm designed to hamper nuclear weapon development in Iran [4]. However, the NHS attack was successful due to not updating a patch that was released by microsoft two months ago. If this attack has taught us anything, it’s that it is vital that updates are deployed as soon as they are available, and that we learn to cope with downtime this sometimes entails.
Our key message for clinicians
Email attachments are an effective way for spreading viruses like ransomware. Do not open attachments unless you know who sent them and you can hold the person sending them accountable. Shutting down computers regularly and letting them update is also a good idea.
If you are ever in doubt, inform your local IT service desk immediately.
It is not enough for clinicians to be digitally complacent anymore. The IT system within your hospital or GP practice is as integral to your service as the bricks and mortar that surround it. You must take as much responsibility for the maintenance of your IT system as you do for infection prevention and control. You must digitally ‘wash your hands’ in the NHS- websites and email attachments are blocked for a reason, and clinicians must adhere to this to avoid spreading viruses.
About the Clinical Developers Club
The Clinical Developers Club is a group of clinicians (including CUXA Founder Dr Gyles Morrison) who code and develop software solutions and projects. Roughly 90% of the club still has active clinical roles within the NHS and code in a number of different languages. They help their members and other clinicians who share the same vision, harness the power of software to improve patient outcomes and the NHS.
References
- https://www.nytimes.com/2016/08/17/us/shadow-brokers-leak-raises-alarming-question-was-the-nsa-hacked.html
- https://technet.microsoft.com/en-us/library/security/ms17-010.aspx
- https://securelist.com/blog/incidents/78351/wannacry-ransomware-used-in-widespread-attacks-all-over-the-world/
[/et_pb_text][/et_pb_column][/et_pb_row][/et_pb_section]


Responses